ENTERPRISE MOBILITY MANAGEMENT
MICROSOFT INTUNE AND AUTOPILOT
Enterprise Mobility Management Made Simple
WHAT WE DO!
We are Microsoft Intune experts, that simple. Protect your corporate data, users and devices with Microsoft Intune MDM.
With Enterprise Mobility + Security we simplify IT by centralizing security management across devices, users, apps and services, safeguard identities and protect corporate data and intellectual property with built in security.
From hand-held iOS and Android devices to Windows 10 workstations or any computer, anywhere in the world, our experienced staff partners with you to create a security blueprint for your organization. We design and implement the solutions, train your staff and help provide the change management services needed to ensure the most successful implementations.
Modern IT with Next Generation PC Management with Microsoft Intune Windows Auto Pilot and co-existence with Configuration Manager named Co-Management.
Next generation PC management creates a lean infrastructure and provides a path to the new Modern IT platform. Let us show you how to reduce network traffic, standardize your environment, simplify administration and reduce costs of traditional PC management.
Let us show how to modernize your Desktop deployment model to a modern, lean and more cost-efficient deployment model. We offer Managed Services for Microsoft Intune.
Quick Services Overview
- Modern Device Management
- Mobile Device Management
- Mobile Application Management
- Windows Information Protection
- Mac OSX Management
- Configuration Manager and Co-management
- Rapid Security POC
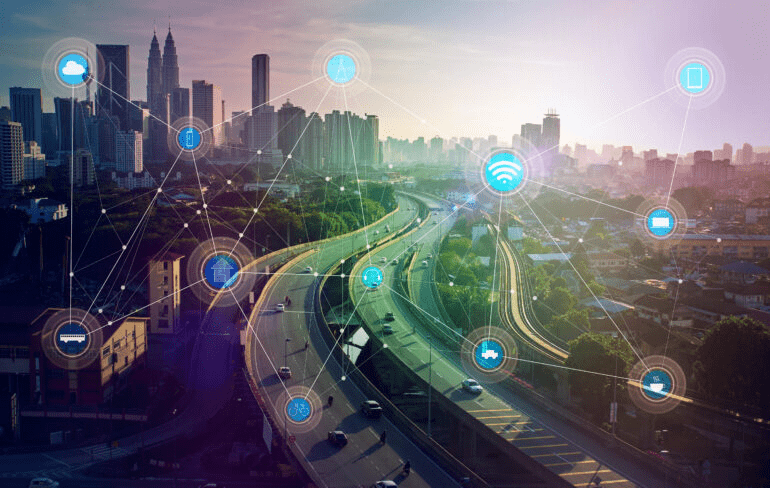
The world just keeps on changing!
With recent world events, companies have had to think fast on their feet with the new forced work from home strategy. Many companies have not been wholly prepared for the need to secure IP on remote corporate and personal devices.
Protecon is helping our clients to change that!
If you need to secure your environment quickly, we are the experts in quick deployments for M365. We make it easy to become secure in at least one day and provide ongoing support to help mature your security needs.

To manage or not to manage BYOD...
Do your users take exception to letting your company fully manage their device? Is it a company policy to legal requirements that you are not allowed to manage a personal device?
Enter Intune App protection!
Intune App protection is a lightweight application management solution as part of Microsoft Intune. All Microsoft productivity applications have a protection SDK integrated with them to protect external cross identity sharing (personal accounts), restricting where users can store data and how they use data.
Do you have a current MDM solution and have M365?
Take advantage of this feature from Microsoft Intune and enhance your current solution as it can be used with any 3rd party EMM solution.
Looking for Windows MAM? Check out Windows Information Protection Below.

To manage or not to manage BYOD...
Do your users take exception to letting your company fully manage their device? Is it a company policy to legal requirements that you are not allowed to manage a personal device?
Enter Intune App protection!
Intune App protection is a lightweight application management solution as part of Microsoft Intune. All Microsoft productivity applications have a protection SDK integrated with them to protect external cross identity sharing (personal accounts), restricting where users can store data and how they use data.
Do you have a current MDM solution and have M365?
Take advantage of this feature from Microsoft Intune and enhance your current solution as it can be used with any 3rd party EMM solution.
Looking for Windows MAM? Check out Windows Information Protection Below.

Protect your windows devices just like MAM (Well Almost)
Microsoft provides another feature within Microsoft Intune under their Intune Application Protection feature called Windows Information Protection (WIP). These cannot be compared side by side because one is for Mobile Devices with different policies to be created and the other is a Windows defined set of policies.
Before you turn this on in your environment, please reach out to Protecon for assistance in developing this correctly. There are many moving parts required to get this set up correctly without without causing user Impact.
Here's some free advise, don't turn on WIP without knowing the details, you could end up blocking users!

Macs are becoming more prevalent in the workspace. Do you have a management plan for them?
As more and more Macs come into the workplace, what can be done to secure them? Do you have a 3rd party solution such as JAMF to manage these? Either way, Microsoft Intune has you covered. From integrations for compliance with current Mac management SaaS services to full on management of Macs, Protecon can get you there.
We provide a recommended best practice configuration from our many years of work. Although we are not Mac experts, we understand the need to provide certain security policies to these Macs in your environment.
Ask Protecon today how we can bring your security vision and compliance vision to your BYOD and Corp Macs!
Have you purchased an M365 plan from Microsoft but are still using a 3rd party Identity provider?
Why not make good use of your investment by migrating from that IDP to Entra ID. Protecon has completed hundreds of migrations from 3rd party IDPs to Entra ID. We employ automation to allow for a relatively quick and painless migration.
We make it simple to get a quote for these services. We send a form that you fill out with the applications that you are using and the requirements for those applications and we can give you a Rough Order of Magnitude within a couple of days.
Some of our automations are from Okta to Microsoft Entra ID which allow us to peer into Okta and automatically create the applications in Entra ID and semi-configure them so 90% of the migration is complete in a matter of days.

Get Secure today with Microsoft EM+S
As part of our Accelerated Rapid Model, one of our feature offerings is a Rapid Security Proof of Concept. This proof of concept allows you to test best practice policies from Protecon from day one of the engagement.
The Rapid Security POC consists of a 5 day workshop to go over the solution, deploy MDM and MAM policies, deep dive into each feature and allow you to start testing the policies that are deployed and give you a much better path forward than figuring it out on your own.


